AMD EPYC “Milan-X” specifications leak out, up to 64 cores, 280W TDP and 768MB L3 cache
https://videocardz.com/newz/amd-epyc-milan-x-specifications-leak-out-up-to-64-cores-280w-tdp-and-768mb-l3-cache
AMD討論POST(69) 睇#1&有時間幫手填資料
Jacksjoke
1001 回覆
3 Like
1 Dislike
Updated Release Date: 10/22/2021
屌
屌

咩事





唔知 本身eta好似係10/12/2021
唔知會唔會再延
唔知會唔會再延

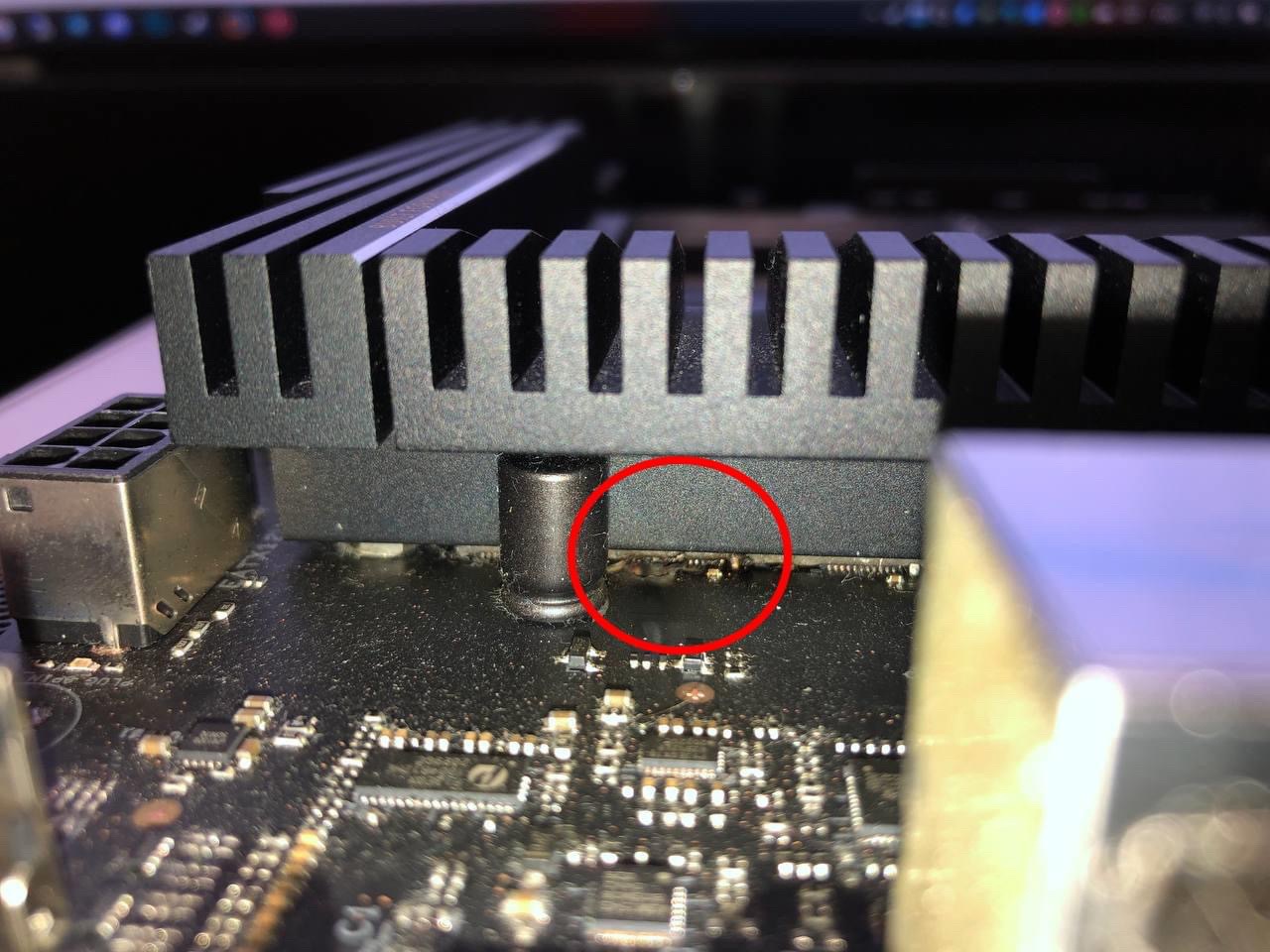
事主拆左板出嚟



AMD Instinct MI300 accelerator might have an Exascale APU mode
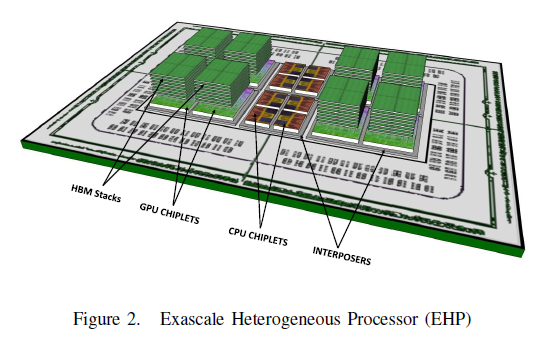
https://videocardz.com/newz/amd-instinct-mi300-accelerator-might-have-an-exascale-apu-mode
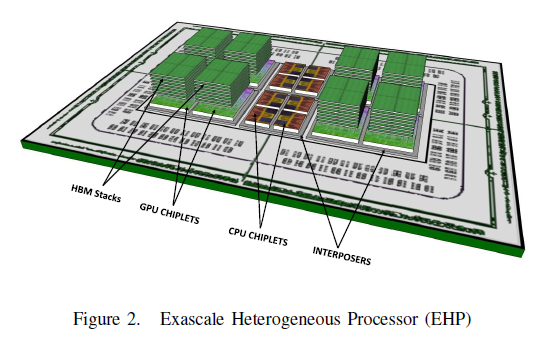
https://videocardz.com/newz/amd-instinct-mi300-accelerator-might-have-an-exascale-apu-mode
AMD: We Stand Ready to Make Arm Chips
AMD's CFO Devinder Kumar recently commented that AMD stands ready to manufacture Arm chips if needed, noting that the company's customers want to work with AMD on Arm-based solutions. Kumar's remarks came during last week's Deutsche Bank Technology Conference, building on comments from AMD CEO Lisa Su earlier in the year that underscored the company's willingness to create custom silicon solutions for its customers, be they based on x86 or Arm architectures. Intel also intends to produce Arm and RISC-V chips, too, meaning that the rise of non-x86 architectures will be partially fueled by the stewards of the dominant x86 ecosystem.
https://www.tomshardware.com/news/amd-we-stand-ready-to-make-arm-chips
AMD's CFO Devinder Kumar recently commented that AMD stands ready to manufacture Arm chips if needed, noting that the company's customers want to work with AMD on Arm-based solutions. Kumar's remarks came during last week's Deutsche Bank Technology Conference, building on comments from AMD CEO Lisa Su earlier in the year that underscored the company's willingness to create custom silicon solutions for its customers, be they based on x86 or Arm architectures. Intel also intends to produce Arm and RISC-V chips, too, meaning that the rise of non-x86 architectures will be partially fueled by the stewards of the dominant x86 ecosystem.
https://www.tomshardware.com/news/amd-we-stand-ready-to-make-arm-chips
Update chippset driver la 



AMD has divulged details about a chipset vulnerability that can allow non-privileged users to read and dump some types of memory pages in Windows. This technique allows an attacker to steal passwords or enable other types of attacks, including circumventing standard KASLR exploitation (aka Spectre and Meltdown) mitigations (via TheRecord).
Word of the bug came as part of a coordinated disclosure with Kyriakos Economou, a security researcher and co-founder of ZeroPeril, who exploited the vulnerability to downloaded several gigabytes of sensitive data from impacted AMD processors — but as a non-admin user. AMD has prepared mitigations that can be downloaded either as part of its latest chipset drivers or by using Windows Update to update the AMD PSP driver (details of how to update are below).
https://www.tomshardware.com/news/amd-chipset-vulnerability-leaks-passwords




AMD has divulged details about a chipset vulnerability that can allow non-privileged users to read and dump some types of memory pages in Windows. This technique allows an attacker to steal passwords or enable other types of attacks, including circumventing standard KASLR exploitation (aka Spectre and Meltdown) mitigations (via TheRecord).
Word of the bug came as part of a coordinated disclosure with Kyriakos Economou, a security researcher and co-founder of ZeroPeril, who exploited the vulnerability to downloaded several gigabytes of sensitive data from impacted AMD processors — but as a non-admin user. AMD has prepared mitigations that can be downloaded either as part of its latest chipset drivers or by using Windows Update to update the AMD PSP driver (details of how to update are below).
https://www.tomshardware.com/news/amd-chipset-vulnerability-leaks-passwords
係咪暫時都冇消息講幾時出zen3既XT款?
有無x570s 主機板推介
暫時睇上 MSI x570s Tomahawk
Budget最多 $2000左右



暫時睇上 MSI x570s Tomahawk
Budget最多 $2000左右



有冇io要求?
應該冇 只有3d cache
應該無 因為太耐無砌機 溫唔切書
諗住俾5900x 用
最多超少少
供電夠 同 塊板唔好過熱就得
諗住俾5900x 用
最多超少少

供電夠 同 塊板唔好過熱就得
用得x570s m.2 有3個係基本


上Giga x570s arous pro ax



上Giga x570s arous pro ax
之前係唔係有個windows 更新會令到打唔到機?
你上左最新版本?
我個Fd用5600x 同3060
應該係windows 最新版本
試過down old version N記drive
一樣打唔到機(隻game會死咗但無死機)
燒furmark 10分鐘左右個furmark就會停咗
應該係windows 最新版本
試過down old version N記drive
一樣打唔到機(隻game會死咗但無死機)
燒furmark 10分鐘左右個furmark就會停咗
試下downgrade 先,都唔得就可能張卡收皮

但我又唔洗用到3條 SSD 既
tomahawk 用料差過arous pro ax?
tomahawk 用料差過arous pro ax?
今代msi x570s : carbon 》tomahawk
Arous pro = carbon
Arous pro = carbon
今代giga x570s🈶️比oc switch
不過如果怕左Giga 形象&強仔保養 就只能msi / Asus
不過如果怕左Giga 形象&強仔保養 就只能msi / Asus
前幾日終於由2700x升做5600x 打機爽勁多 宜家想換走埋張rog 5700xt 真係太熱
宜家想換走埋張rog 5700xt 真係太熱
 宜家想換走埋張rog 5700xt 真係太熱
宜家想換走埋張rog 5700xt 真係太熱
upgrade nv 30 series / amd rx 6000 seriers 





